Vendor Due Diligence Checklist (Free Template)
By The Visualping Team
Updated April 20, 2026
The practical checklist for vendor due diligence: 30 items across 6 categories, depth calibrated by tier, where most programs leak, and a downloadable template. Written for TPRM and procurement practitioners, not for buyers learning the category.
Vendor due diligence is where most TPRM programs spend the most hours and get the least defensible output. Analysts chase SOC 2 reports across 40 vendors, collect half-complete SIG responses, and drop everything into a shared drive that nobody audits. When the board asks how a vendor was evaluated, the program produces a questionnaire response, a copy of the MSA, and a prayer.
There is a better version. It costs less time, produces a defensible artifact, and scales. The rest of this piece is that version: what goes on the checklist, how depth changes by tier, where the common failure modes hide, and where to get the template.
In brief
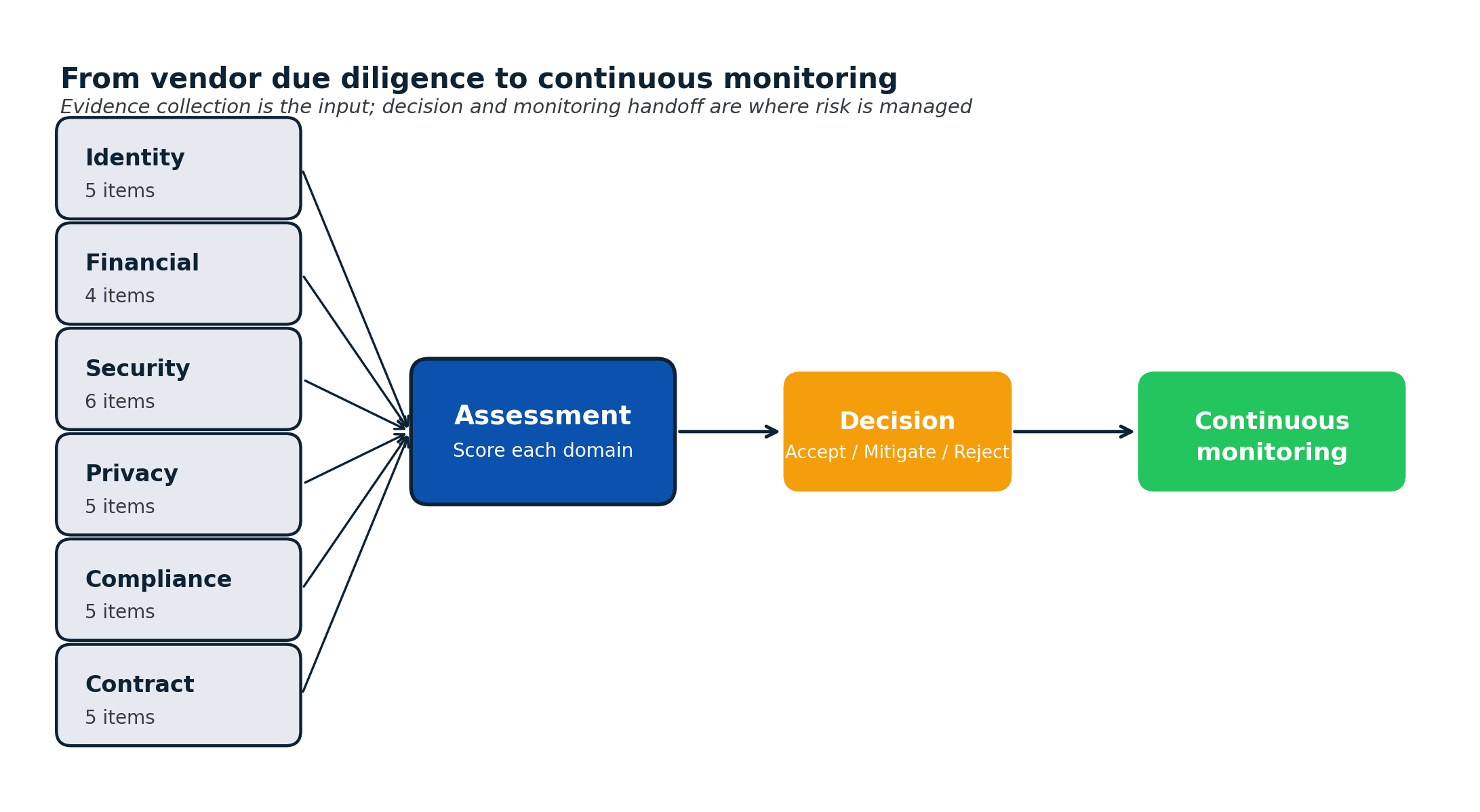
- Vendor due diligence is the evidence-collection step that feeds into vendor risk assessment. It's a specific stage, not the whole process.
- The 30-item checklist spans six categories: identity, financial, security, privacy, compliance, contract.
- Tiering calibrates depth. Tier 1 collects all 30. Tier 2 runs 15 to 20. Tier 3 runs 5 to 6.
- Most programs pull evidence from vendor trust portals rather than sending custom questionnaires. Using an industry standard (SIG Lite, CAIQ) cuts assessment time in half.
- A completed due diligence package is an input, not an output. The assessment decision and the monitoring handoff are where risk actually gets managed.
Vendor due diligence vs related terms
Three terms get used interchangeably and shouldn't be.
- Vendor due diligence: evidence collection. The artifact is a package of documents.
- Vendor risk assessment: evaluation of the evidence against your control requirements. The artifact is a scored decision. The vendor risk assessment guide covers the 5-domain framework and scoring rubric.
- Vendor onboarding: the end-to-end flow from request to go-live that contains both due diligence and assessment as stages. The risk-led vendor onboarding guide covers the 7-stage process.
"Vendor due diligence" is the narrow, evidence-collection step. In most real programs, the same coordinator owns both due diligence and assessment, which is why the terms blur. Separating them clarifies what the checklist below is for: it's the ingestion manifest, not the scoring framework.
When vendor due diligence runs
Six triggers. The first two are calendar-driven; the rest are event-driven.
- Onboarding, before contract execution. The primary moment DD produces value.
- Contract renewal, annually for tier-1 vendors. Refresh the package; verify nothing has expired.
- Scope change: new data categories, new regions, new integrated systems. Triggers a delta DD focused on what's new.
- Incident at the vendor: a breach disclosure, an SEC 8-K, a material press mention. Pull whatever public documentation has been updated since the last review.
- Material change detected in ongoing monitoring: sub-processor addition, DPA amendment, certification lapse, trust center change. This is the connective tissue between DD and continuous monitoring.
- Regulatory trigger: a new obligation (DORA, SEC cyber rule, a state privacy law) that changes what you need to collect from existing vendors.
Programs that handle only triggers 1 and 2 have a three-quarter blind spot. By the time the annual review arrives, half the package is out of date.
The 30-item vendor due diligence checklist
Six categories. Thirty items. The Tier column below shows which tiers each item typically applies to.
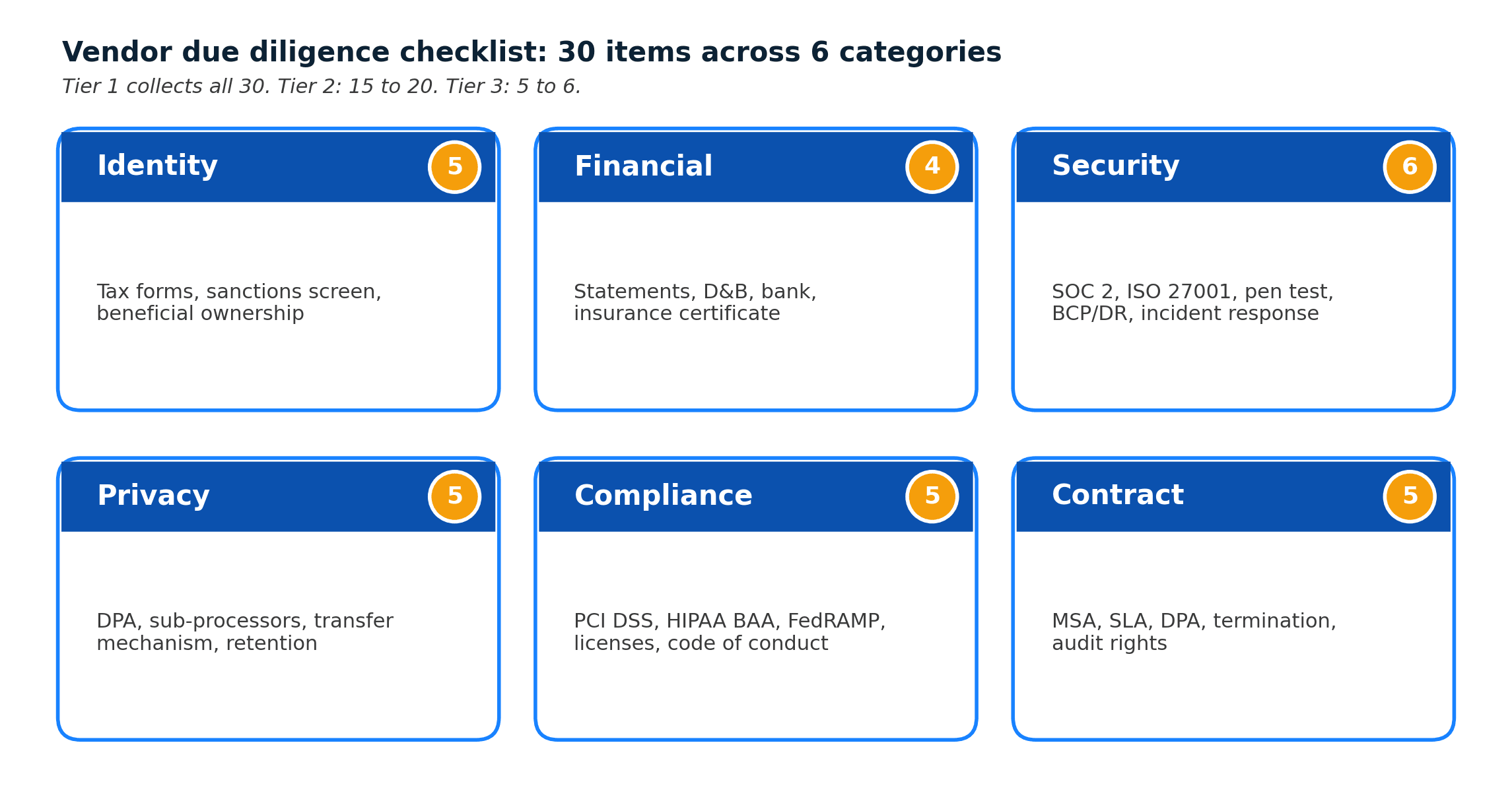
1. Identity and eligibility (5 items)
| # | Item | Tier 1 | Tier 2 | Tier 3 |
|---|---|---|---|---|
| 1 | Legal entity name and registered address | ✓ | ✓ | ✓ |
| 2 | W-9 (US) or W-8 (foreign) tax forms | ✓ | ✓ | ✓ |
| 3 | Certificate of incorporation / business registration | ✓ | ✓ | ✓ |
| 4 | OFAC / sanctions / debarred party screening | ✓ | ✓ | |
| 5 | Beneficial ownership disclosure (for contracts over threshold) | ✓ |
2. Financial (4 items)
| # | Item | Tier 1 | Tier 2 | Tier 3 |
|---|---|---|---|---|
| 6 | Two most recent years of financial statements (audited preferred) | ✓ | ||
| 7 | D&B or equivalent credit score | ✓ | ✓ | |
| 8 | Bank account verification via callback | ✓ | ✓ | |
| 9 | Certificate of insurance naming your company as additional insured | ✓ | ✓ |
3. Security (6 items)
| # | Item | Tier 1 | Tier 2 | Tier 3 |
|---|---|---|---|---|
| 10 | SOC 2 Type II report (within 12 months) | ✓ | ||
| 11 | ISO/IEC 27001 certificate (if applicable) | ✓ | ||
| 12 | Penetration test summary (within 12 months) | ✓ | ||
| 13 | SIG Lite (or CAIQ) questionnaire response for gaps not covered above | ✓ | ✓ | |
| 14 | Business continuity and disaster recovery plan | ✓ | ✓ | |
| 15 | Incident response procedure and breach notification SLA | ✓ | ✓ |
4. Privacy (5 items)
| # | Item | Tier 1 | Tier 2 | Tier 3 |
|---|---|---|---|---|
| 16 | Data Processing Agreement (DPA) signed | ✓ | ✓ | |
| 17 | Current sub-processor list | ✓ | ✓ | |
| 18 | Data transfer mechanism (SCCs, adequacy, equivalent) | ✓ | ✓ | |
| 19 | Privacy policy URL and date of last material update | ✓ | ✓ | |
| 20 | Data retention and deletion schedule | ✓ |
5. Compliance (5 items)
| # | Item | Tier 1 | Tier 2 | Tier 3 |
|---|---|---|---|---|
| 21 | PCI DSS attestation (if vendor touches cardholder data) | ✓ | ||
| 22 | HIPAA BAA executed (if in scope) | ✓ | ||
| 23 | Industry-specific attestations (FedRAMP, HITRUST, regional) | ✓ | ||
| 24 | Applicable regulatory licenses | ✓ | ||
| 25 | Code of conduct and anti-bribery attestation | ✓ | ✓ |
6. Contract (5 items)
| # | Item | Tier 1 | Tier 2 | Tier 3 |
|---|---|---|---|---|
| 26 | Executed MSA | ✓ | ✓ | ✓ |
| 27 | Service level agreement with remedies | ✓ | ✓ | |
| 28 | DPA attached (for vendors processing personal data) | ✓ | ✓ | |
| 29 | Termination and data-return clauses | ✓ | ✓ | |
| 30 | Audit rights and cooperation clauses | ✓ |
Tier 1 collects all 30. Tier 2 collects 15 to 20. Tier 3 collects 5 to 6 (items 1, 2, 3, 26, and sometimes 4). The rubric for what's missing is as important as what's collected.
Commercial vs financial due diligence (and when to do both)
Most TPRM checklists treat due diligence as a single category. Two practitioner distinctions are worth the extra minute.
Financial due diligence (items 6 through 9) asks: will this vendor still exist in 18 months, and is their payment infrastructure legitimate? This matters for long-tail SaaS commitments, for procurement categories with few substitutes, and for any relationship where switching costs are high.
Commercial due diligence (partially items 26 through 30, plus the vendor's customer references and public case studies) asks: does this vendor actually deliver what they claim, at the promised scale, to comparable customers? This is lighter-weight, but it's where real-world reference checks (not just the ones the vendor hand-picks) save you from signal-inflated pitches.
Most TPRM programs skip commercial DD entirely and hope procurement ran it. Procurement often skips it and hopes the business owner did. The result: the vendor relationship goes live without anyone having verified a claim independently.
The evidence collection mechanism: trust portals beat questionnaires
Every vendor DD package has the same structural choice: collect evidence from what the vendor already publishes, or send a custom questionnaire. The first scales; the second doesn't.
Pull first from:
- The vendor's public trust portal (Vanta, SafeBase, Whistic profile).
- The vendor's legal pages: DPA, sub-processor list, privacy policy.
- The vendor's trust center: SOC 2, ISO 27001, pen test summary, certifications.
- Salesforce's public sub-processor page is a concrete example of what "machine-readable vendor evidence" looks like in practice.
Only send a custom questionnaire (SIG Lite, CAIQ, or bespoke) when the public evidence has a gap. For tier-1 vendors touching sensitive data, 3 to 5 custom questions on top of a SIG Lite is often enough.
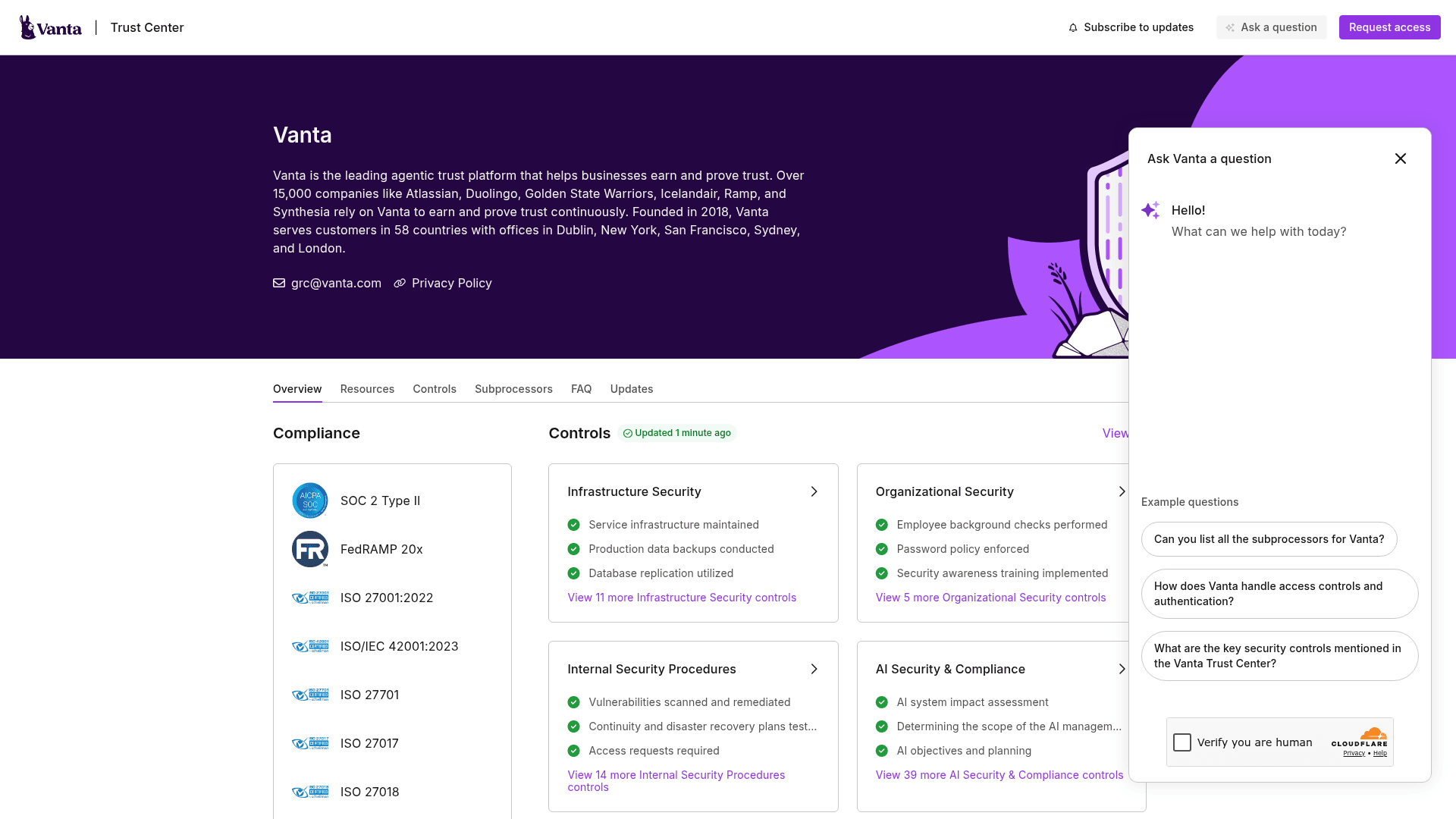
The efficiency gain matters more than it sounds. A vendor asked to generate a fresh 400-question SIG Core takes 2 to 6 weeks. A vendor asked to point to their Vanta profile takes minutes. At 30 new vendors per quarter, that difference is most of your analyst's time.
Depth by tier (and how to actually enforce it)
The 30-item checklist is only useful if it collapses cleanly for tier 2 and tier 3 vendors. Four principles for enforcing that:
- Tier at intake, not at DD. If a tier-3 vendor lands in your analyst's queue and is treated the same as tier 1, the full 30 items get pulled by default. Tier at request stage, then route.
- Make waivers explicit. For tier 1 vendors where a specific item is waived (no PCI scope, for example), document the waiver reason in the package. "Not applicable" without rationale fails an audit.
- Set a gating item per tier. The one thing you won't accept a waiver on. For tier 1: a signed DPA and a current SOC 2 Type II. For tier 2: a signed DPA. For tier 3: executed MSA and W-9/W-8.
- Expire the package. Due diligence collected more than 12 months ago for a tier-1 vendor is stale by default. Require refresh, not just annual review signatures.
Where most vendor due diligence programs leak
Four failure modes account for most of the DD breakage in TPRM programs. Each one is a narrow fix.
The most common is stale SOC 2 references. A vendor submits a SOC 2 Type II with a 9-month reporting period. The report expires. The analyst moves on. Eighteen months later, the package still cites a document that was valid only for one reporting window. Fix: track expiration dates, not just submission dates, and auto-renew the request 30 days before expiry.
The second is sub-processor lists captured at onboarding and never re-fetched. In a sample of 1,132 active sub-processor monitors on our platform, 67% of vendor sub-processor pages logged at least one change in a 90-day window. The DD package you filed three quarters ago describes a sub-processor configuration that no longer exists. Fix: monitor the sub-processor URL on a continuous cadence, not as a DD refresh task.
The third is insurance certificates expiring silently. A vendor's COI is dated. The analyst files it. Ten months later, nobody is watching the expiration. If something goes wrong in month 11, you find out about the lapse during the claim, not before. On our platform, 4,519 active monitors track insurance or certificate-adjacent pages across all use cases, which indicates the scale this control operates at. Fix: monitor the COI page, or require the vendor's insurance portal as an authenticated source with auto-renewal.
The fourth is treating the package as the finish line. A DD package that sits in a shared drive without a risk register entry and a monitoring handoff is not risk management. It's document archival. The package is an input. The decision and the monitoring handoff are where risk actually gets managed.
The template: what to use, what to build
Use an existing vendor due diligence checklist template rather than building one from scratch.
- SIG Lite (Shared Assessments): the industry-standard shorter questionnaire. Use as the core security and privacy evidence pull.
- SIG Core: the full SIG questionnaire. Use for tier-1 vendors in regulated industries.
- CAIQ (Cloud Security Alliance): cloud-native control questionnaire. Use for SaaS and IaaS vendors.
- Your own due diligence manifest: a 1-page document listing which of the 30 items above apply to this vendor at this tier, with status (collected, pending, waived with reason, N/A) and links to where each artifact lives.
Don't rebuild the questionnaire. Do build the manifest. Your manifest encodes your program's specific tier logic and waiver policy. That's the part that should not be generic.
For mid-market programs running 30 to 100 new vendors per quarter, a shared Excel or Airtable structure is enough. Above that scale, the manifest belongs inside your vendor risk management software of record, where it can connect to the risk register and to ongoing monitoring.
Frequently asked questions
What is vendor due diligence?
Vendor due diligence is the evidence-collection step that precedes the vendor risk assessment. It produces a package of documents (SOC 2 reports, DPAs, insurance certificates, financial statements, and so on) that an evaluator uses to score the vendor against your control requirements. In risk-led TPRM programs, due diligence is a distinct stage with a named owner and a clear exit artifact.
What goes in a vendor due diligence checklist?
A complete vendor due diligence checklist covers six categories: identity and eligibility (W-9/W-8, sanctions screening), financial (statements, credit score, insurance), security (SOC 2, ISO 27001, pen test, BCP), privacy (DPA, sub-processor list, transfer mechanism, retention schedule), compliance (PCI, HIPAA, industry attestations), and contract (MSA, SLA, termination, audit rights). A tier-1 vendor's checklist runs about 30 items; tier 2 cuts it to 15 to 20; tier 3 to 5 to 6.
What is the difference between vendor due diligence and vendor risk assessment?
Due diligence is evidence collection. Risk assessment is evaluation of that evidence against your control requirements, producing a scored decision (accept, mitigate, reject). Most programs use one coordinator for both stages, which is why the terms often blur. Separating them clarifies the artifact trail: due diligence produces a package of documents; assessment produces a risk register entry.
How often should vendor due diligence be refreshed?
Tier-1 vendors: annually at minimum, with faster refresh triggered by incidents, scope changes, or material changes detected in continuous monitoring. Tier-2: every 18 to 24 months. Tier-3: on a long cycle or only when triggers fire. Expiration dates on individual artifacts (SOC 2 Type II, insurance certificates, ISO cert validity windows) drive interim refreshes within the larger cycle.
What is know-your-supplier due diligence?
Know-your-supplier (KYS) is the procurement-origin term for the same workflow. It puts extra weight on beneficial ownership disclosure, sanctions screening, and supply-chain risk considerations. KYS is common in manufacturing, banking, and regulated industries. The evidence collected overlaps with vendor DD; the procurement-office framing is the main difference.
What is the 3-vendor rule?
The 3-vendor rule is a procurement sourcing practice requiring at least three qualified vendors to be bid before a selection is made. It is not a due diligence control. It sits upstream of DD, in the sourcing phase, and is waived in narrow-market categories with documentation of why.
Do we need vendor due diligence for every vendor?
No. Tier 3 vendors (commodity services, no data access, low contract value) run a lightweight 5 to 6 item check. Full 30-item DD is reserved for tier-1 vendors with access to regulated or sensitive data, or for long-term relationships where switching costs are high. Tiering at intake is what makes scale workable.
For a program-level view of how this piece fits into the broader lifecycle, frameworks, and operating model, see the full third-party risk management guide.
Where to go next
A complete due diligence package is an input, not an output. The decision that follows it is where risk actually gets managed, and the monitoring that follows the decision is where the picture stays current. The vendor risk assessment guide covers the scoring framework that uses this evidence. The risk-led vendor onboarding guide shows where due diligence fits in the end-to-end flow. For the post-assessment layer, the continuous vendor monitoring guide covers the handoff. For the procurement-side sibling of this checklist aimed at physical suppliers and services, the supplier due diligence workflow covers the procurement lens.
This article summarizes industry practice for vendor due diligence. It is not legal, compliance, or audit advice. Specific regulatory obligations, artifact requirements, and acceptable waiver reasons should be reviewed with your program's TPRM, privacy, legal, and procurement owners before relying on them.
Want to monitor web changes that impact your business?
Sign up with Visualping to get alerted of important updates from anywhere online.
The Visualping Team
The Visualping Team is the content and product marketing group at Visualping, a leading platform for website change detection and competitive intelligence. We write about automation, web monitoring, and tools that help businesses stay ahead.